Intel promises Full Memory Encryption in upcoming CPUs
Companies, agencies, institutions, etc
Intel
SGX (Security Guard Extensions
Intel SGX
Skylake
VM
the Enclave Page Cache
IBM
Software Guard Extensions
TME
MKTME
Multi-Key Total Memory Encryption
Linux
AMD
SEV (Secure Encrypted Virtualization)
SME
AES
RNG
TSME—
BIOS
UEFI
Wayne State University
the University of Houston
ReadingNew
Azure
the Ars Orbital Transmission
CNMN Collection
WIRED Media Group
Condé Nast
People
Jim Salter
Anil Rao
Scott Woodgate
Danny Harnik
Epyc
Ars
Groups
SGX
Physical locations
Intel chips’
Places
No matching tags
Locations
2015—is
128MiB
Rao
Rome
Events
Security Day
Summary
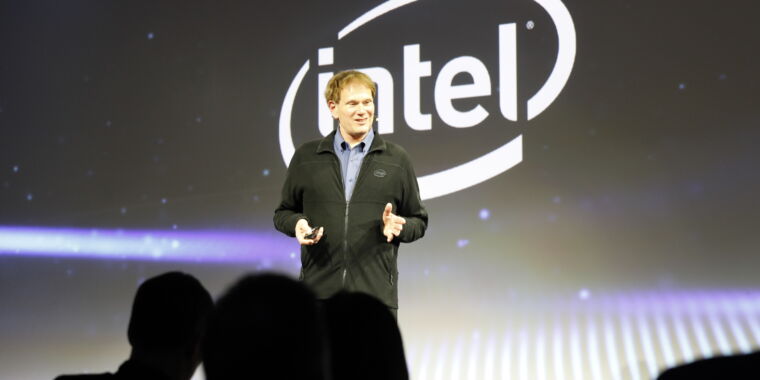
At Intel's Security Day event on Tuesday, the company laid down its present and future vision for security-focused features in its hardware.Intel's Anil Rao and Scott Woodgate opened their presentation with a present-and-future discussion of Intel's SGX (Security Guard Extensions), but their coverage of the company's plans to bring Full Memory Encryption to future Intel CPUs was more interesting.Intel SGX—announced in 2014, and launched with the Skylake microarchitecture in 2015—is one of the first hardware encryption technologies designed to protect areas of memory from unauthorized users, up to and including the system administrators themselves. As an entire-system feature, TSME is enabled or disabled in system BIOS (or UEFI), and it requires no special planning on the part of application developers—once enabled, everything's encrypted, and that's all there is to say about it.AMD's approach to memory encryption also involves far less performance impact than Intel SGX. In a 2018 presentation, researchers from Wayne State University and the University of Houston showed most workloads entirely unimpacted by Secure Encryption Virtualization (a subset of AMD's SME that allows whole-VM encryption, with a separate key used for each covered virtual machine), despite significant performance impacts with Intel's SGX.Since Intel's TME and MKTME are—for the moment—still hypothetical, it's too soon to make any bold predictions about what their performance impact will be.
As said here by Jim Salter