Telegram messages are a focus in newly uncovered hack campaign from Iran
Companies, agencies, institutions, etc
Android
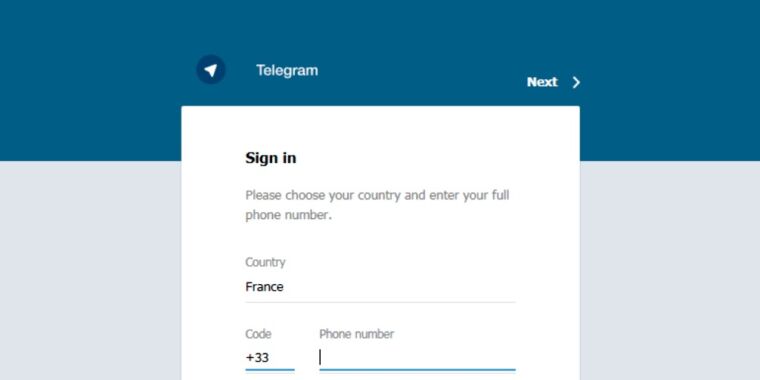
Telegram
Microsoft Office
Fake Telegram
the Telegram for Windows
Updater.exe
the Miaan Group
WhatsApp
Check Point
KeePass
the Ars Orbital Transmission
CNMN Collection
WIRED Media Group
Condé Nast
People
Dan Goodin
Rampant Kitten
Android
Miaan
Ars
Groups
Iranian
Android
Persian
Iranians
Physical locations
the Middle East
Places
No matching tags
Locations
Sweden
Iran
victims’
the Islamic Republic
Events
No matching tags
Summary
Check Point said evidence from passive DNS records—which log other domains that have used the same IP address used in Rampant Kitten—suggested that the attackers have been active since at least 2014.A separate report published by the Miaan Group, a human rights organization that focuses on digital security in the Middle East, echoed the research and added details, including the exfiltration of the malware of data from the WhatsApp messenger.“Since early 2018, Miaan researchers have been tracking malware used in a series of cyberattacks on Iranian dissidents and activists,” organization researchers wrote. “The research has uncovered hundreds of victims of malware and phishing attacks that stole data, passwords, personal information, and more.” It wasn’t clear if that malware included the infostealers detailed by Check Point.Readers should remember that the ability to extract Telegram, KeePass, or WhatsApp data from an infected computer isn’t automatically an indication of especially sophisticated malware or a flaw in the targeted applications.
As said here by Dan Goodin